How to Reduce Your Attack Surface: A Practical Guide for Organizations
Every asset your organization exposes to the internet is an invitation. A forgotten subdomain. An employee email in a breach database. A staging server that was supposed to be temporary three years ago. An OAuth token granting access to a service nobody remembers integrating.
Attackers do not need sophisticated exploits to find these. They use the same public data sources available to anyone — DNS records, certificate transparency logs, search engines, breach databases, and social media. And they do it systematically, continuously, at scale.
Reducing your attack surface is not about deploying more security tools. It is about shrinking the number of things that need protecting in the first place. Every domain you decommission, every exposed service you lock down, every leaked credential you rotate — removes an opportunity that an attacker would otherwise exploit.
This guide covers the practical, actionable steps organizations use to reduce their attack surface — from auditing domains and cleaning up employee data exposure to eliminating shadow IT and establishing the continuous monitoring that prevents the surface from growing back.
Whether you are a security team lead hardening your organization’s perimeter, an IT manager responsible for infrastructure hygiene, or a consultant assessing a client’s external exposure — this is the systematic approach that actually works.
What Is an Attack Surface and Why Does It Keep Growing?
Your attack surface is the sum of all points where an unauthorized user could attempt to enter or extract data from your environment. In the context of internet-facing exposure, it includes every domain, subdomain, IP address, open port, web application, API endpoint, email address, exposed document, and third-party integration that is reachable from the public internet.
The reason attack surfaces grow is simple: organizations add things faster than they remove them.
A marketing team launches a campaign microsite and never takes it down. A developer spins up a staging environment on a subdomain and forgets about it after the feature ships. An acquisition brings in dozens of domains with unknown configurations. Employees sign up for SaaS tools using their work email, creating accounts that persist long after the tool is abandoned.
Each of these creates exposure. Not because the asset itself is necessarily vulnerable, but because it exists — discoverable, potentially misconfigured, and almost certainly unmonitored.
The Asymmetry Problem
The fundamental challenge in reducing your attack surface is asymmetry. Adding exposure is easy and fast — anyone in the organization can register a subdomain, deploy a cloud service, or create an account on a third-party platform. Removing exposure requires discovery, verification, coordination with asset owners, and careful decommissioning.
This asymmetry means that without deliberate effort, attack surfaces only grow. The average organization’s external footprint is significantly larger than what appears in any internal asset inventory. Research consistently shows that organizations discover 30 to 80 percent more external-facing assets when they first conduct comprehensive external attack surface management — and many of those unknown assets represent genuine security risks.
External vs. Internal Attack Surface
While internal attack surface reduction — network segmentation, endpoint hardening, access control — is important, this guide focuses on the external attack surface: everything visible from outside your network without any credentials or internal access.
The external surface matters disproportionately because it is where attacks begin. An attacker who discovers a vulnerable external asset does not need to bypass your firewall, evade your endpoint detection, or compromise an employee first. They simply connect directly to the exposed service and exploit it.
This is why reducing your attack surface externally delivers outsized security returns compared to almost any other investment.
Step 1: Audit Your Domains and DNS Assets
Domain and DNS hygiene is the single most impactful place to start when you want to reduce your attack surface. Your domains are the root of your external presence — every subdomain, every DNS record, every service they point to is part of the surface attackers will enumerate.
Inventory Everything You Own
Start by building a complete inventory of every domain your organization has ever registered. This is harder than it sounds. Domains accumulate through:
- Marketing campaigns — microsites, landing pages, and vanity domains
- Product launches — separate domains for individual products or services
- Geographic expansion — country-code TLDs for regional operations
- Acquisitions — domains inherited from acquired companies
- Defensive registrations — typosquatting domains registered to prevent abuse
- Employee registrations — domains registered by individuals for work-related projects
Check your domain registrar accounts, but do not stop there. Reverse WHOIS lookups using your organization’s name, email addresses, and known registrant details can uncover domains you did not know about. Certificate transparency logs reveal subdomains that have had SSL certificates issued — including ones that may not appear in your DNS anymore but still exist in public records.
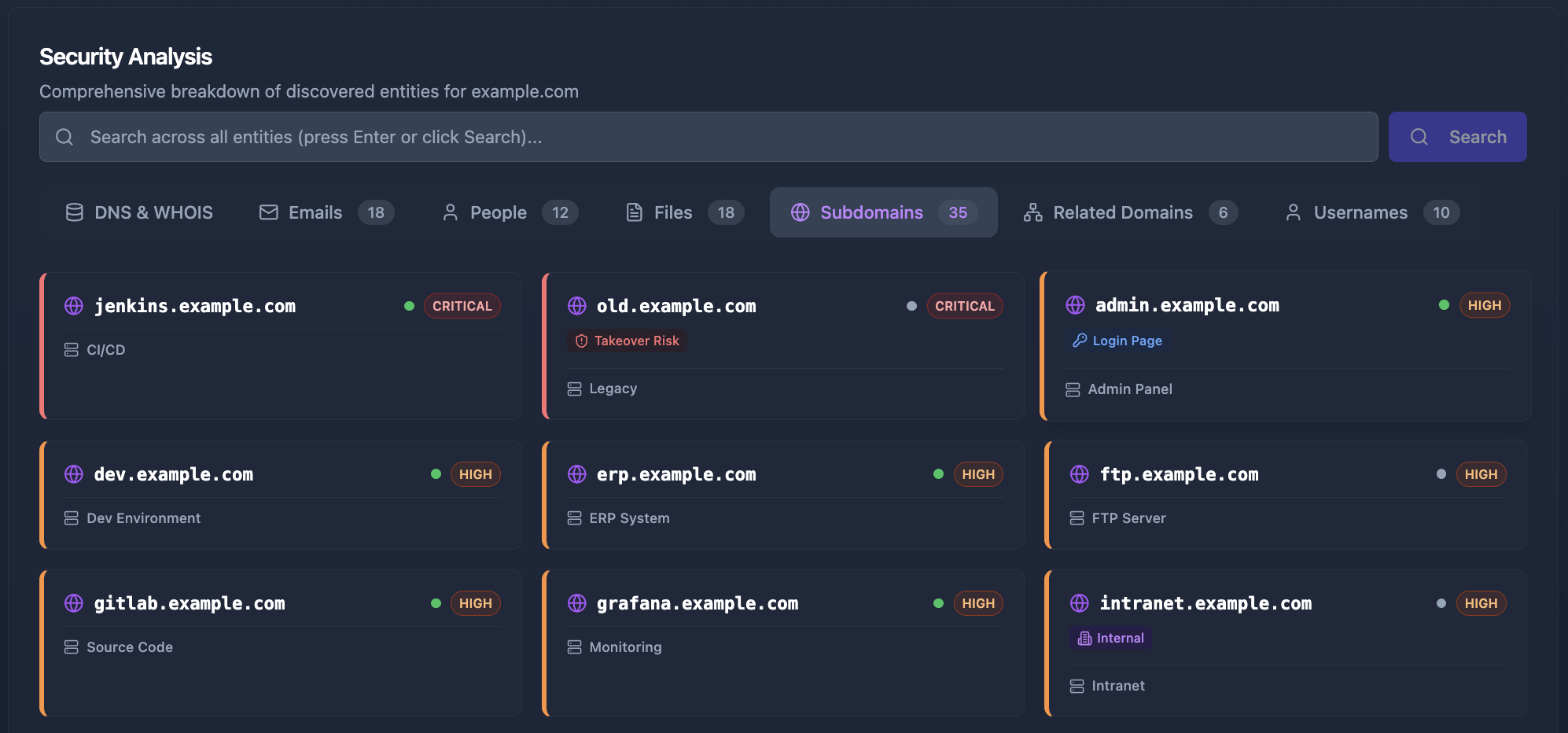
Cyborux automates this discovery process — enter your primary domain and it maps subdomains, DNS records, and associated infrastructure automatically, surfacing assets that manual auditing would miss.
Hunt for Dangling DNS Records
Dangling DNS records are one of the most dangerous and underappreciated attack vectors. They occur when a DNS record (typically a CNAME) points to a service that no longer exists. The classic scenario:
- Your team creates
blog.example.comas a CNAME pointing to a third-party blogging platform - The team cancels the blogging service but forgets to remove the DNS record
- An attacker registers the same account name on the blogging platform
- The attacker now controls content served under your trusted domain
This is subdomain takeover, and it is alarmingly common. Any DNS record pointing to a decommissioned cloud service — Azure, AWS, GitHub Pages, Heroku, Shopify, or dozens of other platforms — is potentially vulnerable.
For a technical deep dive into subdomain discovery methods that help identify these risks, see our complete guide to subdomain enumeration.
Action items:
- Enumerate all DNS records for every domain you control
- Identify CNAME records pointing to external services
- Verify that every external service is still active and under your control
- Remove DNS records for any service that has been decommissioned
- Establish a process requiring DNS cleanup as part of service decommissioning
Consolidate and Decommission
Not every domain you own needs to exist. Audit your domain portfolio and ask: does this domain serve a current business purpose? If not, it is adding to your attack surface without adding value.
- Redirect unused domains to your primary site rather than letting them resolve to nothing (or worse, to expired hosting)
- Transfer domains from individual employee accounts to organizational registrar accounts
- Let expire domains you no longer need, after verifying they are not referenced anywhere critical — but only if the domain has no residual brand value that a squatter could exploit
- Consolidate subdomains by migrating services from standalone domains to paths under your primary domain where appropriate
Every domain you remove is an entire branch of attack surface eliminated — all its subdomains, all its DNS records, all its associated services.
Step 2: Clean Up Exposed Employee Data
People are consistently the weakest point in an organization’s security posture — not because employees are careless, but because their personal data is scattered across the internet in ways the organization never intended and often does not know about.
The Email-to-Breach Pipeline
An employee’s work email address is the starting point for a well-understood attack chain:
- Email discovery — the attacker finds employee emails through company websites, LinkedIn, GitHub commits, document metadata, or OSINT techniques
- Breach database lookup — the attacker checks whether the email appears in known data breaches (it usually does — the average professional email has appeared in multiple breaches)
- Credential correlation — if the breach includes passwords and the employee reuses passwords, the attacker now has valid credentials
- Platform enumeration — tools can determine which online services an email is registered on, revealing the employee’s digital footprint
- Social engineering — armed with knowledge of the employee’s role, interests, and online accounts, the attacker crafts targeted phishing
Every step in this chain relies on publicly available information. Reducing your attack surface at the employee data level means interrupting this chain at as many points as possible.
Practical Steps for Employee Data Reduction
Minimize public email exposure:
- Use role-based addresses (
sales@,support@,press@) on public-facing pages instead of personal employee emails - Remove or restrict staff directory pages that list individual email addresses
- Train employees to use separate personal emails for non-work online accounts
- Audit GitHub repositories and other public code sources for hardcoded employee email addresses in commit histories
Monitor breach databases:
- Regularly check whether employee emails appear in new breach datasets using services like Have I Been Pwned
- Implement mandatory password resets when employee credentials appear in breaches
- Deploy credential monitoring as a continuous process, not a one-time check
Manage social media exposure:
- Provide employees with clear guidance on privacy settings for LinkedIn, Twitter, and other platforms
- Consider the information value of publicly visible organizational charts and reporting structures
- Train employees to recognize social engineering attempts that leverage information from their public profiles
Control document metadata:
- PDF, Word, and Excel documents often contain metadata revealing author names, email addresses, internal file paths, and software versions
- Strip metadata from documents before publishing them externally
- Audit documents currently hosted on your domains for metadata exposure using Google dork queries like
site:yourdomain.com filetype:pdf
Step 3: Discover and Eliminate Shadow IT
Shadow IT — technology adopted by employees or teams without IT or security approval — is one of the fastest-growing sources of attack surface expansion. It is also one of the hardest to address because, by definition, nobody in security knows it exists.
Why Shadow IT Proliferates
Shadow IT is not a failure of policy. It is a consequence of organizational velocity. Teams adopt tools because they need to move fast:
- A marketing team signs up for a project management SaaS because the approved tool does not fit their workflow
- A developer deploys a test environment on a personal cloud account because the procurement process for a company cloud instance takes weeks
- A sales team integrates a third-party enrichment API using company credentials because the integration makes their pipeline more efficient
- An executive uses an unauthorized file-sharing service to collaborate with an external partner
Each of these decisions is rational from the individual’s perspective. But each one creates unmanaged exposure — an account using corporate credentials, a service with access to company data, and potentially an internet-facing asset with no security monitoring.
Finding Shadow IT from the Outside
Traditional approaches to shadow IT detection rely on network monitoring, CASB (Cloud Access Security Broker) tools, or endpoint agents. These are valuable but limited — they only see traffic that flows through managed infrastructure.
External discovery finds shadow IT from the attacker’s perspective by looking for signals that are visible from the public internet:
- DNS records pointing to unauthorized cloud services
- SSL certificates issued for subdomains associated with shadow deployments
- Technology fingerprinting that reveals SaaS services exposing company data
- Google dorking that surfaces indexed content from unauthorized services
- Email registrations on platforms where employees signed up using company addresses
This is exactly the kind of comprehensive, automated discovery that Cyborux performs. Enter your domain and the platform identifies subdomains, exposed services, email registrations, and indexed files — including shadow IT deployments that no internal tool would detect because they exist entirely outside your managed infrastructure.
Addressing Shadow IT Without Killing Productivity
The goal is not to ban all unauthorized tools — that approach fails because it ignores the legitimate needs that drove adoption. Instead:
- Inventory what exists through external and internal discovery
- Assess the risk of each shadow IT instance (what data does it have access to? what credentials are involved?)
- Migrate high-risk shadow IT to approved, managed alternatives
- Formalize low-risk shadow IT by bringing it under IT management
- Streamline the procurement process so teams can get approved tools faster than they can sign up for unauthorized ones
Step 4: Audit and Harden Third-Party Integrations
Every third-party service connected to your infrastructure extends your attack surface beyond your direct control. API keys, OAuth tokens, webhook URLs, and service integrations create pathways that attackers can exploit — especially when they are misconfigured or forgotten.
The Supply Chain Attack Surface
Third-party risk is not theoretical. Some of the most significant breaches in recent years have originated through compromised vendors, exploited API integrations, or abused OAuth grants. Your organization’s security is effectively limited by the security of every service you connect to.
Conducting a Third-Party Integration Audit
Map all integrations:
- OAuth grants and authorized applications in your identity provider
- API keys issued for external services
- Webhook URLs that receive data from your systems
- SAML and SSO connections
- DNS TXT records that verify third-party service ownership (these are visible externally and confirm what services you use)
- Calendar, email, and collaboration tool integrations
Evaluate each integration:
- Is this service still in active use?
- Does the integration have the minimum necessary permissions (least privilege)?
- When was the API key or OAuth token last rotated?
- Does the third party have a security certification (SOC 2, ISO 27001)?
- What data does this integration have access to?
Remediate:
- Revoke access for integrations that are no longer in use
- Reduce permissions to the minimum required for active integrations
- Implement regular key rotation schedules
- Remove DNS TXT verification records for decommissioned services
- Document all active integrations with clear ownership
Zero Trust for Integrations
Apply the same zero trust principles to third-party integrations that you apply to internal access:
- Never grant permanent, broad access when temporary, scoped access will work
- Monitor API usage patterns and alert on anomalies
- Require MFA for administrative access to integration platforms
- Maintain the ability to revoke any integration instantly if the vendor is compromised
Step 5: Secure Your Cloud and Infrastructure Exposure
Cloud services are the fastest-growing component of most organizations’ attack surfaces. The ease of provisioning cloud resources — a key business advantage — is also a security challenge because it means new exposure can appear in minutes without security review.
Common Cloud Exposure Patterns
- Public storage buckets (S3, Azure Blob, GCS) with overly permissive access controls
- Exposed management interfaces — cloud dashboards, Kubernetes dashboards, and CI/CD pipelines accessible from the internet
- Default credentials on cloud-deployed applications and services
- Overly permissive security groups allowing inbound traffic from any source
- Unused cloud resources — instances, load balancers, and endpoints that remain running after their purpose has ended
- Misconfigured CDN origins that bypass security controls
Cloud Attack Surface Reduction Checklist
- Audit public access: Verify every cloud resource that is accessible from the internet. If it does not need to be public, restrict it.
- Review security groups and firewall rules: Remove rules that allow broad inbound access. Apply the principle of least privilege to network access.
- Scan for default credentials: Check every internet-facing service for default or weak authentication.
- Enable cloud-native security controls: Use AWS Security Hub, Azure Defender, or GCP Security Command Center to continuously monitor configuration.
- Tag and track: Implement mandatory tagging for cloud resources so every asset has a known owner, purpose, and expected lifetime.
- Automate decommissioning: Set up automated cleanup for resources tagged as temporary that exceed their expected lifetime.
Step 6: Prioritize Based on Real Risk
Not all attack surface is created equal. A forgotten marketing microsite serving static HTML is less urgent than an exposed administration panel with default credentials, which is less urgent than a breached employee credential granting access to your VPN.
Reducing your attack surface effectively requires prioritization, because most organizations have more exposed assets than they can remediate simultaneously.
Risk Assessment Framework
Evaluate each exposure across four dimensions:
1. Exploitability — How easy is it for an attacker to exploit this exposure?
- A publicly accessible admin panel with default credentials: critical
- A subdomain serving a static page with no dynamic content: low
- An employee email found in a breach database with a reused password: critical
2. Impact — What happens if this exposure is exploited?
- Access to customer data: high
- Defacement of a secondary marketing page: low
- Lateral movement into production infrastructure: critical
3. Exposure Level — How visible is this to attackers?
- Indexed by Google: high visibility
- Only discoverable through DNS enumeration: moderate visibility
- Requires brute-forcing or guessing: lower visibility
4. Remediation Effort — How hard is it to fix?
- Removing a DNS record: minutes
- Rotating credentials and updating all dependent services: hours to days
- Migrating a legacy application off a vulnerable platform: weeks to months
Building a Remediation Roadmap
Use your risk assessment to create a prioritized remediation plan:
- Immediate (this week): Exposed credentials, admin panels with default authentication, dangling DNS records at risk of subdomain takeover
- Short-term (this month): Unused services and domains, shadow IT with company data, unpatched internet-facing applications
- Medium-term (this quarter): Third-party integration cleanup, employee data exposure reduction, cloud configuration hardening
- Ongoing: Continuous monitoring, policy enforcement, regular re-assessment
Discover your full attack surface in minutes
Cyborux maps your external exposure automatically — subdomains, emails, exposed files, technologies, and more. Enter your domain. No agents, no configuration, no complexity.
See Your ExposureStep 7: Establish Continuous Monitoring
Here is the uncomfortable truth about reducing your attack surface: it is never finished. Even if you remediate every exposure today, new ones will appear tomorrow. A developer deploys a test service. An employee signs up for a new SaaS tool. A third-party vendor changes their infrastructure. A data breach exposes credentials that were rotated internally but not on external platforms.
Attack surface reduction without continuous monitoring is a snapshot — accurate at the moment it was taken and increasingly outdated with every passing day.
Why Annual Assessments Are Not Enough
The traditional model — quarterly vulnerability scans, annual penetration tests — was designed for environments that changed slowly. Modern organizations do not change slowly. Cloud resources are provisioned in minutes. New subdomains appear daily. Employee onboarding and offboarding create continuous changes in credential exposure.
The gap between assessments is where risk accumulates. An asset that appears on Monday and is exploited on Wednesday will not be caught by a scan scheduled for Friday — let alone one scheduled for next quarter.
What Continuous Monitoring Should Cover
Effective continuous monitoring for attack surface reduction tracks:
- New subdomains and DNS changes — detecting when new records appear or existing ones change
- Certificate issuance — monitoring certificate transparency logs for new SSL certificates under your domains
- Breach database updates — detecting when employee credentials appear in newly published breach datasets
- Technology changes — identifying when internet-facing services update software versions (which may introduce or resolve vulnerabilities)
- Search engine indexing — detecting when sensitive pages or documents are newly indexed by Google
- Port and service changes — identifying when new services start listening on internet-facing IP addresses
Automated vs. Manual Monitoring
Manual monitoring — running tools periodically and reviewing results — works for small environments but does not scale. As your domain portfolio grows, the number of assets to track grows exponentially (each domain can have hundreds of subdomains, each subdomain can run multiple services).
Automated platforms handle this scale by running discovery continuously and alerting on changes. This is the approach Cyborux takes — comprehensive reconnaissance running automatically so your team focuses on responding to findings rather than generating them. Instead of maintaining a collection of scripts, wordlists, and scheduling infrastructure, you get continuous visibility through a single interface.
For organizations building their own monitoring capabilities, our guide to IT asset discovery tools covers the open-source and commercial options available.
Step 8: Build Organizational Processes That Prevent Regrowth
Technical controls are necessary but not sufficient. Without organizational processes, every remediated exposure will eventually reappear in a different form. New employees will create new shadow IT. New projects will launch new subdomains. New vendors will require new integrations.
Embed Security in Asset Lifecycle Management
Every digital asset should have a defined lifecycle with security checkpoints:
Creation:
- Security review before any new domain, subdomain, or internet-facing service goes live
- Mandatory documentation of purpose, owner, expected lifetime, and data classification
- Baseline security configuration applied automatically (HTTPS, security headers, access controls)
Operation:
- Regular verification that the asset is still needed and properly maintained
- Automated monitoring for configuration drift, vulnerability exposure, and unauthorized changes
- Clear escalation paths when monitoring detects issues
Decommissioning:
- Defined process for taking assets offline that includes DNS cleanup, credential revocation, and data removal
- Verification that decommissioning is complete (no dangling references)
- Audit trail documenting what was removed and when
Create Clear Ownership
One of the most common reasons attack surfaces grow unchecked is that nobody owns the problem. Subdomains are created by developers, managed by operations, and never reviewed by security. The fix is simple but requires organizational commitment:
- Every internet-facing asset has a named owner
- Owners are responsible for the security posture of their assets
- Orphaned assets (no identifiable owner) are flagged for review and potential decommissioning
- Ownership transfers are documented when people change roles or leave the organization
Train for Security Awareness
Technical controls prevent exploitation. Training prevents the exposure from being created in the first place:
- Teach employees why using work emails for personal online accounts expands the organization’s attack surface
- Explain the risk of shadow IT and provide clear, fast paths to approved alternatives
- Include attack surface awareness in onboarding for technical teams — developers and DevOps engineers need to understand the security implications of the infrastructure they provision
- Run periodic phishing simulations that leverage real OSINT findings to demonstrate the practical risks of data exposure
Common Mistakes When Reducing Your Attack Surface
Even well-intentioned attack surface reduction programs can go wrong. These are the most common pitfalls:
Focusing on Quantity Over Risk
Remediating 100 low-risk exposures while ignoring 5 critical ones creates a false sense of progress. Risk-based prioritization ensures your limited remediation capacity is spent where it matters most. A single exposed admin panel with default credentials is more dangerous than 50 forgotten marketing subdomains serving static content.
Treating It as a One-Time Project
Attack surface reduction is a continuous process, not a project with a start and end date. Organizations that conduct a one-time audit, remediate findings, and then move on will find their attack surface has grown back within months. Build ongoing monitoring and periodic review into your security operations — not your project portfolio.
Ignoring the Human Element
Technical scanning finds technical exposures. But the most damaging attack vectors often run through people — phishing, credential stuffing, social engineering. A comprehensive approach to reducing your attack surface includes employee data exposure alongside infrastructure exposure.
Creating Friction Without Providing Alternatives
Locking down shadow IT and restricting third-party integrations without providing approved alternatives drives workarounds. Employees who cannot get the tools they need through official channels will find unofficial channels — and the unofficial channels are always less secure. Pair every restriction with a viable alternative.
Neglecting Acquired Assets
Mergers and acquisitions are attack surface explosions. Every acquired company brings its own domains, subdomains, cloud resources, employee accounts, and third-party integrations. Many organizations run thorough technical due diligence before an acquisition but fail to actually remediate the findings after the deal closes. Treat acquisition integration as a critical attack surface reduction project with defined timelines and accountability.
Measuring Attack Surface Reduction
What gets measured gets managed. Track these metrics to demonstrate progress and identify areas needing attention:
Key Metrics
- Total external assets — domains, subdomains, IP addresses, and services discoverable from the internet (trending down is good)
- Unknown assets discovered — assets found through external discovery that were not in your internal inventory (this number should decrease over time as your processes improve)
- Mean time to discovery — how long between a new asset appearing and your team knowing about it (shorter is better)
- Mean time to remediation — how long between discovering an exposure and resolving it (shorter is better)
- Credential exposure count — number of employee credentials currently present in breach databases (should decrease through rotation and awareness)
- Shadow IT instances — count of unauthorized services discovered per quarter (should decrease as processes mature)
- Dangling DNS records — count of DNS records pointing to non-existent services (should be zero)
Reporting to Leadership
Security leadership and board-level stakeholders care about risk reduction, not technical details. Frame your attack surface reduction program in terms of:
- Risk reduction — “We eliminated 47 exposed services, including 3 with critical vulnerabilities that could have led to data access”
- Coverage improvement — “Our asset inventory now covers 95% of our external footprint, up from 60% before the program”
- Process maturity — “New assets are now detected within 24 hours of creation, down from an average of 90 days”
- Comparison — benchmark your external exposure against industry peers or previous assessments
Tools and Approaches for Attack Surface Reduction
The right tooling depends on your team’s size, technical capabilities, and the complexity of your environment.
Manual + Open Source
For small environments or technically skilled teams, a combination of open-source tools provides solid coverage:
- Subdomain enumeration: Amass, Subfinder, crt.sh queries
- DNS analysis: dig, nslookup, DNSRecon
- Technology fingerprinting: Wappalyzer, httpx, WhatWeb
- Email discovery: theHarvester, Hunter.io
- Credential monitoring: Have I Been Pwned API
- Google dorking: Manual queries or automated with tools like pagodo
The challenge is coordination. Running six different tools, correlating their outputs, scheduling regular scans, and maintaining the infrastructure requires significant ongoing effort. This approach works for periodic assessments but struggles to deliver the continuous monitoring that modern attack surfaces demand.
Automated Platforms
Automated external attack surface management platforms consolidate discovery, analysis, and monitoring into a single workflow:
- Single-step onboarding — enter a domain and get comprehensive results
- Correlated findings — subdomains linked to IP addresses linked to technologies linked to vulnerabilities
- Continuous monitoring — automatic re-scanning and change detection
- Prioritized output — risk-scored findings rather than raw data dumps
Cyborux is built for this exact use case. Enter your domain and the platform automatically runs subdomain enumeration, email discovery, technology fingerprinting, Google dorking, WHOIS analysis, and breach monitoring — then correlates the results into a unified view of your external exposure. No agents to deploy, no infrastructure to manage, no wordlists to maintain. Results in minutes, not days.
This approach is particularly valuable for organizations that need comprehensive external visibility but lack the resources to build and maintain a custom toolchain — security consultancies managing multiple client domains, IT teams at growing companies, and compliance-focused organizations that need continuous evidence of attack surface monitoring.

Hybrid Approach
Many mature security programs use both. Open-source tools handle deep, targeted investigations — penetration testing engagements, incident response scenarios, specific threat hunting. Automated platforms provide the continuous baseline monitoring that ensures nothing slips through between manual assessments.
The key is that some form of continuous external monitoring is non-negotiable. The gap between periodic assessments is exactly where undetected exposure accumulates — and where attackers find their way in.
Frequently Asked Questions
What is the most effective way to reduce your attack surface?
Start with asset discovery — you cannot reduce what you do not know about. Most organizations significantly underestimate the size of their external attack surface. Run comprehensive discovery against all your domains to establish a baseline, then prioritize remediation based on risk. The highest-impact actions are typically removing dangling DNS records, decommissioning unused services, and rotating credentials found in breach databases.
How often should we scan for attack surface changes?
Continuously, if possible. The traditional model of quarterly or annual assessments misses the majority of changes in modern, cloud-heavy environments. At minimum, run external discovery monthly and supplement with continuous monitoring of DNS changes, certificate transparency logs, and breach databases. The goal is to reduce your time-to-discovery — the gap between when an asset appears and when your security team knows about it.
Does reducing the attack surface replace the need for vulnerability management?
No. Attack surface reduction and vulnerability management are complementary. Reducing your attack surface eliminates unnecessary exposure — assets and services that do not need to exist. Vulnerability management addresses weaknesses in the assets that remain. Think of attack surface reduction as removing unnecessary doors and windows from a building, and vulnerability management as ensuring the remaining doors and windows have strong locks.
How do we handle attack surface growth from mergers and acquisitions?
Treat every acquisition as an attack surface expansion event. Before closing the deal, run external discovery against the target company’s domains to understand what you are inheriting. After closing, immediately integrate the acquired company’s assets into your monitoring program. Prioritize remediating critical findings (exposed credentials, dangling DNS records, unpatched services) within the first 30 days. Full integration of the acquired attack surface into your ongoing management program should be a defined workstream with clear ownership and timelines.
What is the relationship between digital footprint and attack surface?
Your digital footprint is all information about your organization that is publicly accessible on the internet. Your attack surface is the subset of that footprint that could be exploited by an attacker. Reducing your digital footprint directly reduces your attack surface — less public information means fewer entry points, less intelligence for social engineering, and fewer assets to monitor and protect. Every piece of unnecessary public exposure you eliminate is one fewer tool in an attacker’s reconnaissance toolkit.
Can small organizations benefit from attack surface reduction?
Absolutely. Smaller organizations often have larger relative attack surfaces because they lack the dedicated security staff to manage asset hygiene. A 50-person company with three forgotten subdomains, employee emails in breach databases, and undiscovered shadow IT has proportionally as much unmanaged exposure as a Fortune 500 enterprise — but far fewer resources to detect and remediate it. Automated platforms that require minimal setup and maintenance are particularly valuable for smaller teams that need external visibility without dedicated security operations infrastructure.
Final Thoughts
Reducing your attack surface is not glamorous work. There are no zero-day exploits to discover, no sophisticated attackers to outwit, no dramatic incident response scenarios. It is the methodical process of finding what is exposed, deciding what should not be, and removing it — then repeating that process continuously.
But it is arguably the highest-value security activity an organization can perform. Every asset you remove from your external attack surface is one fewer thing to monitor, patch, configure, and defend. Every credential you rotate after finding it in a breach database is one fewer credential an attacker can try. Every dangling DNS record you clean up is one fewer subdomain takeover waiting to happen.
The organizations that get breached through unknown external assets are not the ones without security budgets. They are the ones without visibility. They have firewalls, vulnerability scanners, endpoint detection, and incident response plans — but they do not know about the forgotten staging server, the shadow IT deployment, or the employee credential that has been sitting in a breach database for two years.
Visibility is the prerequisite. Everything else — vulnerability management, threat detection, incident response, compliance — depends on knowing what exists. And knowing what exists requires looking from the outside in, the same way an attacker would.
Cyborux is built for exactly this. Enter your domain and the platform maps your external exposure — subdomains, emails, exposed files, technologies, and more — automatically and continuously. No tools to chain together, no scripts to maintain, no results to manually correlate. Just the visibility you need to start reducing what does not need to be there.
Start with your domains. Discover what is out there. Prioritize based on risk. Remediate systematically. Monitor continuously. And build the organizational processes that prevent regrowth.
Your attackers are already mapping your external exposure. The question is whether you are doing it first.