Subdomain Enumeration: Methods, Tools, and Why It Matters for Security
Every domain has a story it does not tell on the surface. Behind a company’s main website sit dozens — sometimes hundreds — of subdomains: staging servers, internal dashboards, forgotten microsites, API endpoints, and development environments. Each of these subdomains is a separate attack surface that may have its own vulnerabilities, misconfigurations, and exposure risks.
Subdomain enumeration is the systematic process of discovering all subdomains associated with a target domain. It is one of the most critical steps in security assessments, penetration testing, and external attack surface management — because you cannot secure what you cannot see, and subdomains are where visibility gaps hide.
The challenge is that most organizations significantly underestimate the number of subdomains they operate. A company that believes it has 20 subdomains may actually have 200 when you account for test environments created by developers, marketing landing pages, legacy applications, acquired company assets, and cloud services provisioned outside of IT oversight. Each undiscovered subdomain is a potential entry point that receives zero security monitoring.
This guide covers everything you need to know about subdomain enumeration: why it matters, how passive and active techniques work, which tools deliver the best results, how to defend against subdomain takeover, and how to build a continuous monitoring program that keeps pace with your organization’s changing infrastructure.
What Is Subdomain Enumeration?
Subdomain enumeration is the process of identifying all subdomains that exist under a given domain. A subdomain is a prefix added to a root domain — for example, mail.example.com, dev.example.com, or api.staging.example.com are all subdomains of example.com.
From a DNS perspective, each subdomain can resolve to a different IP address, run a different application, and be managed by a different team. This means that an organization’s security posture is only as strong as its weakest subdomain. A hardened main website means nothing if dev.example.com is running an unpatched application with default credentials.
Subdomain discovery serves multiple purposes depending on who is performing it:
- Penetration testers enumerate subdomains to map the target’s attack surface and identify the most promising entry points for further exploitation.
- Security teams use subdomain enumeration to maintain visibility into their organization’s external footprint and detect unauthorized or misconfigured services.
- Bug bounty hunters rely on comprehensive subdomain discovery to find assets that other researchers may have missed, increasing their chances of discovering vulnerabilities.
- Compliance teams need subdomain inventories to ensure all public-facing assets meet regulatory requirements for security controls and data protection.
The key insight is that subdomain enumeration is not a one-time exercise. Organizations create and decommission subdomains constantly. A developer provisions a staging environment on Monday, a marketing team launches a campaign microsite on Wednesday, and a contractor sets up a file-sharing service on Friday — all potentially without the security team’s knowledge. Continuous enumeration is the only way to maintain an accurate picture.
Why Subdomain Enumeration Matters for Security
The security implications of undiscovered subdomains extend far beyond theoretical risk. Real-world breaches regularly trace back to forgotten or unmonitored subdomains that provided attackers with their initial foothold.
The Hidden Attack Surface
Most organizations focus their security investments on their primary web applications — the customer-facing sites that generate revenue and handle sensitive data. But attackers do not limit their reconnaissance to www.example.com. They systematically enumerate every subdomain, looking for the weakest link.
What they typically find is alarming:
- Development and staging environments running outdated software versions with debug mode enabled, verbose error messages, and default credentials
- Internal tools accidentally exposed to the internet — monitoring dashboards, CI/CD pipelines, database administration panels, and project management systems
- Legacy applications that were replaced but never decommissioned, still running on old infrastructure with unpatched vulnerabilities
- Cloud services provisioned by individual teams without security review, often misconfigured with overly permissive access controls
- Abandoned marketing sites and campaign-specific landing pages that were never taken down after the campaign ended
Each of these represents a real, exploitable attack vector. And because they are not part of the organization’s primary security monitoring, breaches through these entry points often go undetected for extended periods.
Breach Statistics and Real-World Impact
The data consistently shows that unknown and unmanaged assets are a leading cause of security incidents. Research from major cybersecurity firms finds that organizations discover 30 to 80 percent more external assets than they knew about when running comprehensive asset discovery for the first time. Many of these assets are subdomains with significant security issues.
High-profile incidents have demonstrated the consequences:
- Subdomain takeover attacks have affected major technology companies, financial institutions, and government agencies — allowing attackers to serve malicious content or steal credentials under a trusted domain name
- Exposed staging environments have leaked production database credentials, API keys, and customer data
- Forgotten admin panels with default credentials have provided direct access to production systems
- Unmonitored subdomains have been used to host phishing pages that bypass email security filters because they originate from a trusted domain
Compliance and Regulatory Implications
Regulatory frameworks are increasingly explicit about the need for comprehensive asset inventories that include all publicly facing infrastructure:
- PCI DSS 4.0 requires identification and inventory of all system components in the cardholder data environment, including public-facing web applications
- ISO 27001 mandates identification and management of information assets, which includes subdomains and associated services
- NIST Cybersecurity Framework places asset management (ID.AM) as a foundational function
- GDPR requires organizations to know where personal data is processed — including on subdomains they may not be actively tracking
Organizations that cannot demonstrate awareness of their complete subdomain landscape face audit findings, compliance gaps, and increased liability in the event of a breach.
Passive Subdomain Enumeration Techniques
Passive enumeration methods discover subdomains without sending any traffic to the target’s infrastructure. This makes them stealthier, safer, and particularly valuable as a first step — they reveal what is publicly known without triggering security alerts or rate limits.
Certificate Transparency Logs
Certificate Transparency (CT) is the single most reliable passive source for subdomain discovery. CT is a public framework that requires certificate authorities to log every SSL/TLS certificate they issue into publicly auditable logs. When an organization provisions a certificate for staging.example.com, that subdomain becomes permanently recorded in CT logs — regardless of whether it is linked from any webpage.
Services like crt.sh provide free, searchable access to CT log data. A single query for %.example.com returns every certificate ever issued for any subdomain under that domain. This reveals:
- Active subdomains with current certificates
- Historical subdomains whose certificates have expired but may still be accessible
- Wildcard certificates that indicate the presence of dynamic subdomain infrastructure
- Internal service names that reveal organizational structure and technology stack
CT log monitoring is also valuable for real-time subdomain detection. By continuously watching CT logs, security teams can detect new subdomains within minutes of a certificate being issued — often before the service is fully deployed. This provides an early warning mechanism for unauthorized or misconfigured services.
Passive DNS Databases
Passive DNS services aggregate historical DNS resolution data collected from recursive resolvers, ISP partnerships, and other sources. Unlike active DNS queries, passive DNS reveals historical records — subdomains that existed in the past, even if they have been removed from current DNS configuration.
Key passive DNS providers include SecurityTrails, VirusTotal, and Farsight DNSDB. These databases are particularly valuable for discovering:
- Subdomains that were recently deleted but may still be accessible via cached DNS entries or direct IP access
- Historical infrastructure changes that reveal patterns in how the organization manages its domain
- IP address associations that help identify related infrastructure and hosting providers
- DNS record types beyond A records — including MX, TXT, CNAME, and SRV records that reveal mail servers, verification tokens, and internal service architectures
Search Engine Indexing
Search engines crawl and index content across the web, including content hosted on subdomains. Using targeted search operators, security professionals can discover subdomains that appear in search results:
site:example.com -wwwreveals indexed pages on subdomains other than the main websitesite:*.example.comfinds content across all indexed subdomains- Cached versions of removed pages may reveal subdomains that are no longer linked
While search engines only index subdomains that serve web content, they can reveal subdomains that the organization may have forgotten about — particularly marketing sites, documentation portals, and legacy applications.
Web Archive Analysis
The Wayback Machine and similar web archiving services store historical snapshots of websites, including pages that link to subdomains. Analyzing archived content reveals:
- Subdomains referenced in old navigation menus, footer links, and sitemap files
- API endpoints and service URLs embedded in archived JavaScript code
- Internal hostnames accidentally exposed in archived error messages or debug output
- Historical infrastructure that was replaced but never fully decommissioned
Web archive analysis is a powerful complement to other passive techniques because it captures subdomain references that may no longer exist in current, live content.
WHOIS and Reverse DNS
While WHOIS records primarily provide domain registration information, they can support subdomain discovery in several ways:
- Reverse WHOIS lookups identify other domains registered by the same organization, expanding the scope for subdomain enumeration
- Name server analysis reveals which DNS providers the organization uses, which can inform active enumeration strategies
- Reverse DNS (PTR records) on discovered IP addresses can reveal additional hostnames and subdomains
These techniques are most valuable when combined with other passive methods to build a comprehensive picture of an organization’s domain infrastructure before moving to active enumeration.
Passive Discovery Pipeline
──────────────────────────────────────────────
┌──────────┐ ┌──────────┐ ┌──────────┐ ┌──────────┐
│ CT Logs │ │ Passive │ │ Search │ │ Web │
│ crt.sh │ │ DNS │ │ Engines │ │ Archives │
│ Censys │ │ VT / ST │ │ Dorks │ │ Wayback │
└────┬─────┘ └────┬─────┘ └────┬─────┘ └────┬─────┘
│ │ │ │
└────────────┴─────┬──────┴────────────┘
▼
┌─────────────────────────────────────────┐
│ Merged & Deduplicated Subdomain List │
└─────────────────────────────────────────┘
Active Subdomain Enumeration Techniques
Active enumeration involves directly interacting with the target’s DNS infrastructure and web servers. These techniques are more thorough than passive methods alone but generate network traffic that may be detected or rate-limited.
DNS Brute-Forcing
DNS brute-forcing is the most common active enumeration technique. It works by systematically resolving potential subdomain names against the target’s DNS servers to determine which ones exist.
The process involves:
- Generating candidate subdomain names from wordlists containing common prefixes (dev, staging, api, admin, test, internal, vpn, mail, ftp, etc.)
- Resolving each candidate by querying DNS for
candidate.example.com - Identifying valid subdomains when the DNS query returns a response (A record, CNAME, etc.) rather than NXDOMAIN
- Recursive enumeration by applying the same wordlist to discovered subdomains (e.g., if
api.example.comexists, testv1.api.example.com,staging.api.example.com, etc.)
The effectiveness of DNS brute-forcing depends heavily on the quality and size of the wordlist. General-purpose wordlists like those from SecLists contain thousands of common subdomain prefixes. Targeted wordlists based on the organization’s technology stack, industry, and naming conventions produce better results.
Performance considerations are critical for DNS brute-forcing at scale. Modern tools use concurrent DNS resolution with configurable rate limits to test thousands of candidates per second while respecting DNS server capacity. Using multiple DNS resolvers (public resolvers like Google, Cloudflare, and Quad9) distributes the query load and avoids being blocked by a single resolver.
DNS Zone Transfers
A DNS zone transfer (AXFR) is a mechanism designed for replicating DNS records between authoritative name servers. When a DNS server is misconfigured to allow zone transfers from arbitrary sources, an attacker can request the complete zone file — revealing every DNS record in the domain at once.
While zone transfer misconfigurations have become less common as DNS security awareness has improved, they still occur, particularly in:
- Legacy DNS infrastructure that has not been updated
- Internal DNS servers accidentally exposed to the internet
- Test or development DNS servers with permissive configurations
Testing for zone transfers is quick and straightforward. A successful zone transfer provides the most complete subdomain inventory possible from a single query — but the chance of success is low on well-maintained infrastructure.
Permutation and Alteration Scanning
Permutation scanning generates variations of known subdomains to discover related assets. Once initial enumeration reveals a set of subdomains, permutation scanning creates candidates by:
- Appending common suffixes:
dev→dev1,dev2,dev-new,dev-old - Prepending common prefixes:
api→api-staging,api-internal,api-v2 - Substituting common patterns:
staging→stg,stage,uat,preprod - Combining discovered subdomains: if
apiandstagingboth exist, testapi-staging,staging-api,api.staging - Incrementing numbers:
web1→web2,web3,web4
This technique is highly effective because organizations tend to follow consistent naming conventions. If you find app1.example.com, there is a strong probability that app2.example.com and app3.example.com also exist.
Tools like dnsgen and altdns specialize in permutation-based subdomain discovery, often uncovering assets that wordlist-based brute-forcing misses.
Virtual Host Discovery
Not all subdomains have unique IP addresses. Multiple subdomains can share a single IP address, differentiated by the Host header in HTTP requests. Virtual host (vhost) discovery sends HTTP requests with different Host headers to a known IP address to identify which subdomains are served from it.
This technique is particularly effective for:
- Shared hosting environments where many subdomains resolve to the same server
- Cloud-hosted applications behind load balancers
- CDN configurations where multiple sites share edge infrastructure
- Internal applications accessible from specific IP addresses
Virtual host discovery can reveal subdomains that do not have public DNS records at all — services that are intended to be internal but are accessible to anyone who knows the correct Host header.
Subdomain Enumeration Tools: From Open-Source to Automated Platforms
The subdomain enumeration ecosystem ranges from specialized command-line tools to comprehensive platforms that automate the entire process. Choosing the right tool depends on your objectives, technical expertise, and operational requirements.
Open-Source Command-Line Tools
The open-source community has produced several powerful tools that are widely used in security assessments:
Subfinder is a fast, passive subdomain discovery tool that aggregates results from dozens of data sources including CT logs, search engines, passive DNS databases, and web archives. It is designed for speed and can enumerate thousands of subdomains in seconds. Subfinder is passive-only, making it safe to run without risk of triggering target alerts.
Amass by OWASP is the most comprehensive open-source subdomain enumeration tool available. It combines passive data collection, active DNS brute-forcing, permutation scanning, and reverse DNS resolution into a single framework. Amass supports dozens of data sources and provides network mapping capabilities that go beyond simple subdomain discovery.
Sublist3r is a lightweight Python tool that queries search engines (Google, Bing, Yahoo, Baidu) and services like VirusTotal and crt.sh to discover subdomains. It is simpler than Amass but effective for quick enumerations.
Knockpy combines DNS brute-forcing with passive data sources and supports wildcard detection, which is critical for avoiding false positives on domains that respond to all queries.
Massdns is a high-performance DNS stub resolver designed for bulk lookups. While it does not generate subdomain candidates itself, it is often used as a backend resolver for other tools, capable of resolving millions of domains per hour.
Commercial and Enterprise Solutions
Enterprise security teams often need more than command-line tools can provide. Commercial platforms offer:
- Continuous monitoring with automated scheduling and alerting
- Historical tracking that shows how the subdomain landscape changes over time
- Risk assessment that classifies discovered subdomains by exposure level
- Integration with vulnerability scanners, SIEMs, and ticketing systems
- Collaboration features for team-based security operations
Automated OSINT Platforms
The most efficient approach to subdomain enumeration is using platforms that automate the entire discovery workflow — combining multiple passive and active techniques, correlating results, eliminating duplicates, and presenting findings with actionable context.
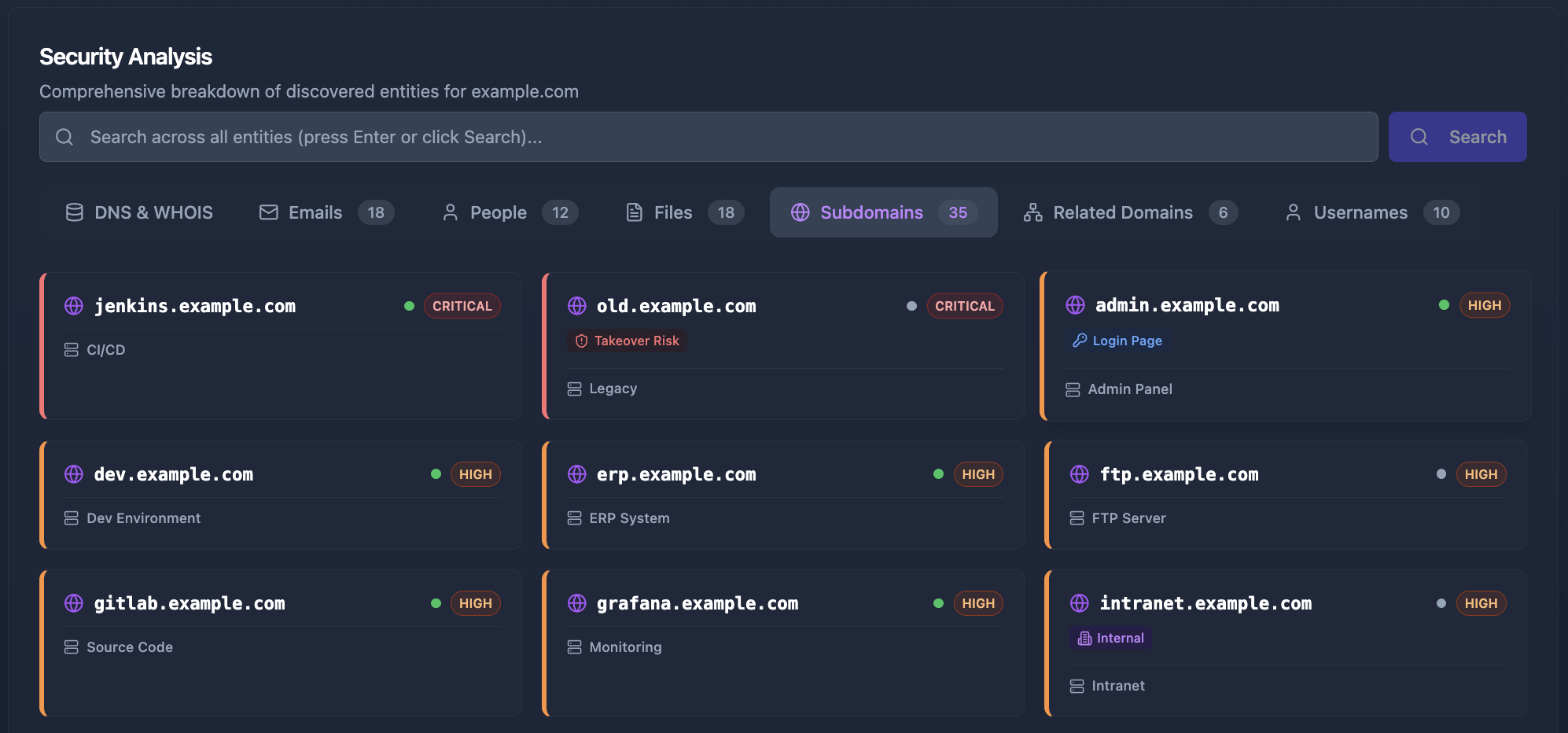
Cyborux exemplifies this approach. Instead of manually configuring and running multiple command-line tools, piping outputs between them, and deduplicating results, Cyborux automates the entire process from a single seed domain. Enter your domain, and the platform runs subdomain enumeration alongside OSINT techniques, email discovery, technology fingerprinting, and Google dorking — delivering a comprehensive view of your external attack surface in minutes, not hours.
This automated approach is particularly valuable for:
- Security teams that need continuous visibility without dedicating analyst time to running manual tools
- IT managers who need to understand their organization’s external exposure without deep security expertise
- Consultants who need fast, repeatable results across multiple client engagements
Subdomain Takeover: The Critical Risk You Cannot Ignore
Subdomain takeover is one of the most dangerous risks associated with unmonitored subdomains. It occurs when a subdomain’s DNS record points to an external service that is no longer active — allowing an attacker to claim that service and serve content under your trusted domain.
How Subdomain Takeover Works
The attack follows a predictable pattern:
- An organization creates
blog.example.comand configures a CNAME record pointing to a third-party service (e.g.,example-blog.herokuapp.comorexample.s3-website.amazonaws.com) - The organization later stops using the service and deletes its account — but forgets to remove the CNAME DNS record
- An attacker discovers the dangling CNAME through subdomain enumeration
- The attacker creates a new account on the third-party platform and claims the unclaimed hostname
- The attacker now controls content served at
blog.example.com
Because the subdomain belongs to the organization’s trusted domain, the attacker’s content inherits that trust:
- Phishing pages at
blog.example.comwill pass many email security filters - Session cookies scoped to
.example.commay be accessible to the attacker - SEO reputation of the parent domain gives attacker content search engine credibility
- SSL certificates can be issued for the subdomain via automated providers like Let’s Encrypt
Services Commonly Vulnerable to Takeover
Not all third-party services are equally susceptible. Takeover is possible when a service allows new users to claim a hostname that was previously registered by another account. Commonly vulnerable services include:
- GitHub Pages — Custom domain can be claimed by any GitHub user
- Heroku — App names can be re-registered after deletion
- AWS S3 — Bucket names are globally unique and can be re-created
- Azure — Various services including App Service, Traffic Manager, and CloudApp
- Shopify — Custom domains can be configured by any store
- Fastly, Cloudfront, and other CDNs — Custom domain associations can be re-created
- Zendesk, Freshdesk, and other SaaS platforms — Custom domain configurations
Detection and Prevention
Defending against subdomain takeover requires both proactive enumeration and ongoing monitoring:
Detection:
- Regularly enumerate all subdomains and check CNAME records for dangling references
- Test whether CNAME targets respond with service-specific “not found” pages (indicating the service account has been deleted)
- Monitor for new CNAME records that point to external services
- Use tools like subjack, nuclei, or can-i-take-over-xyz to automate takeover detection
Prevention:
- Remove DNS records immediately when decommissioning external services
- Maintain an inventory of all CNAME records and their associated service accounts
- Implement DNS change monitoring to alert when records are modified
- Use CAA (Certificate Authority Authorization) records to restrict which CAs can issue certificates for your domain
- Consider using a wildcard CNAME to a controlled service as a catch-all for unused subdomains
How a Subdomain Takeover Works
Service Decommissioned
Company cancels Heroku app but forgets to remove the DNS record
CNAME Left Dangling
old.example.com CNAME still points to app.herokuapp.com
Attacker Claims It
Attacker registers app.herokuapp.com and now controls the subdomain
Stop guessing what subdomains you have
Cyborux discovers every subdomain, email, exposed file, and service across your domain — automatically. No tools to install, no scripts to maintain. Enter your domain and get results in minutes.
See Your ExposureBest Practices for Subdomain Security
Discovering subdomains is only the first step. Organizations need disciplined practices to manage their subdomain landscape and reduce their digital footprint over time.
Establish a Subdomain Inventory
Maintain a living document or database that tracks every subdomain your organization operates. For each entry, record:
- Purpose — What the subdomain is used for
- Owner — Which team or individual is responsible for it
- Technology stack — What software and services it runs
- Sensitivity level — Whether it handles sensitive data, credentials, or internal information
- External dependencies — Any third-party services it relies on (CNAME targets, CDN configurations, etc.)
- Expiration or review date — When the subdomain should be reassessed for continued need
This inventory should be the authoritative source of truth for your subdomain landscape. Any discrepancy between the inventory and actual DNS records should trigger investigation.
Implement Continuous Monitoring
Point-in-time subdomain enumeration scans become stale quickly. New subdomains can appear daily as developers, marketing teams, and third-party vendors provision services. Continuous monitoring ensures that new subdomains are detected and assessed promptly.
Effective continuous monitoring includes:
- CT log monitoring to detect new certificates issued for your domain
- Passive DNS monitoring to identify new DNS records
- Scheduled active enumeration to catch subdomains that do not have certificates
- Alerting that notifies the security team when new or unexpected subdomains appear
The goal is to reduce the time to discovery — the gap between when a subdomain is created and when the security team knows about it. In mature organizations, this gap is measured in minutes. In others, it can be months.
Enforce DNS Hygiene
Poor DNS management is the root cause of most subdomain security issues. Enforce practices that keep your DNS configuration clean:
- Remove DNS records for decommissioned services immediately — do not leave dangling CNAMEs
- Use descriptive naming conventions that make it easy to identify a subdomain’s purpose and owner
- Restrict DNS management access to authorized personnel and require change approval workflows
- Audit DNS records periodically to identify records that no longer serve a purpose
- Implement DNSSEC where possible to prevent DNS spoofing and cache poisoning
- Set appropriate TTL values that balance performance with the ability to make rapid changes during incidents
Secure Development and Staging Environments
Development and staging subdomains are among the most common sources of security exposure. They frequently run with relaxed security controls — debug mode enabled, verbose error messages, default credentials, and outdated dependencies. Protect these environments by:
- Restricting access with IP allowlists, VPN requirements, or authentication
- Using non-obvious naming — avoid predictable names like
dev,staging, ortestthat appear in every brute-forcing wordlist - Never using production data in development environments without proper anonymization
- Applying the same security baseline (HTTPS, authentication, patching) as production environments
- Setting expiration dates on temporary environments and automatically decommissioning them
Leverage Wildcard Certificates Carefully
Wildcard certificates (*.example.com) simplify certificate management but have security implications for subdomain enumeration:
- Wildcards do not appear in CT logs for individual subdomains, reducing passive discovery visibility
- A compromised wildcard certificate private key exposes all subdomains simultaneously
- Wildcard certificates can mask the creation of unauthorized subdomains since no new certificate issuance triggers a CT log entry
If using wildcard certificates, supplement CT monitoring with active DNS enumeration to ensure comprehensive visibility.
Building a Continuous Subdomain Monitoring Program
Moving from ad-hoc subdomain enumeration to a continuous monitoring program requires a structured approach.
Phase 1: Baseline Discovery
Start by running comprehensive enumeration against all your known root domains using both passive and active techniques. Combine results from CT logs, passive DNS, search engines, brute-forcing, and permutation scanning. Deduplicate the results and validate that each discovered subdomain actually resolves and serves content.
This baseline becomes your starting inventory. Document every subdomain, identify its owner and purpose, and flag any that are unexpected or potentially risky.
Phase 2: Risk Assessment
For each discovered subdomain, assess:
- Exposure level — Is it accessible from the internet? Does it require authentication?
- Technology risk — Is it running outdated software? Are there known vulnerabilities?
- Data sensitivity — Does it process or store sensitive information?
- Takeover risk — Does it use CNAME records pointing to external services?
- Compliance relevance — Does it fall within scope of regulatory requirements?
Prioritize remediation based on risk. An exposed admin panel with default credentials on a production database is an immediate priority. A static marketing page with no dynamic functionality is a lower concern.
Phase 3: Continuous Monitoring
Deploy automated monitoring that runs on a regular cadence:
- Daily CT log monitoring for new certificates
- Daily passive DNS checks for new or changed records
- Weekly active brute-force enumeration with updated wordlists
- Immediate alerting for high-risk indicators (new CNAME records, exposed admin panels, dangling DNS references)
Phase 4: Integration with Security Operations
Connect your subdomain monitoring outputs to your broader security program. New subdomains should automatically be:
- Added to your vulnerability scanner’s target list
- Assessed for technology stack and known vulnerabilities
- Monitored by your SIEM for security events
- Tracked in your asset management system with ownership metadata
Platforms like Cyborux streamline this entire workflow by handling enumeration, correlation, and risk assessment automatically — allowing security teams to focus on remediation rather than data collection.
Common Mistakes in Subdomain Enumeration
Even experienced security professionals make mistakes that lead to incomplete or misleading enumeration results. Avoid these common pitfalls:
Relying on a Single Technique
No single enumeration method finds everything. CT logs miss subdomains that use wildcard certificates. Passive DNS misses recently created subdomains. Brute-forcing misses subdomains with unusual names not in wordlists. Search engines only find subdomains with indexed web content.
The fix: Always combine at least three to four different enumeration techniques. Cross-reference results and investigate discrepancies.
Ignoring Wildcard DNS
Some domains are configured with wildcard DNS records (*.example.com → 1.2.3.4), meaning every possible subdomain name returns a valid response. Without wildcard detection, brute-forcing tools will report thousands of false positives.
The fix: Test for wildcard DNS before beginning brute-force enumeration. Generate several random, long subdomain names and check if they resolve. If they do, the domain uses wildcard DNS, and your enumeration methodology must account for it — typically by comparing response IP addresses and filtering out those matching the wildcard.
Enumerating Only Once
A subdomain landscape is not static. New subdomains appear daily. Running enumeration once and considering the job done leaves a growing blind spot over time.
The fix: Implement continuous monitoring as described above. At minimum, run comprehensive enumeration monthly and supplement with daily CT log monitoring.
Not Validating Results
Raw enumeration output often contains stale records, parked domains, and entries that no longer serve live content. Treating unvalidated enumeration output as a definitive inventory leads to wasted effort on non-existent assets and missed attention on actual risks.
The fix: Validate every discovered subdomain by checking DNS resolution, HTTP response codes, and content. Classify results as active, inactive, or redirecting to focus investigation efforts appropriately.
Overlooking Non-Standard Ports
Many services run on non-standard ports (8080, 8443, 3000, 9090, etc.). Discovering a subdomain but only checking ports 80 and 443 misses a significant portion of the attack surface.
The fix: After subdomain discovery, perform port scanning on discovered hosts to identify services running on non-standard ports.
Frequently Asked Questions
What is the difference between subdomain enumeration and DNS enumeration?
DNS enumeration is a broader term that covers discovering all types of DNS records (A, AAAA, MX, NS, TXT, SRV, CNAME, etc.) for a domain. Subdomain enumeration specifically focuses on discovering hostnames (subdomains) under a domain. In practice, subdomain enumeration uses DNS enumeration as one of its techniques, but also incorporates non-DNS sources like CT logs, search engines, and web archives.
Is subdomain enumeration legal?
Subdomain enumeration using passive techniques (CT logs, passive DNS, search engines) is legal in most jurisdictions because it only accesses publicly available information. Active techniques like DNS brute-forcing involve sending queries to DNS servers, which is generally legal but may violate terms of service for certain DNS providers if done at excessive volume. When performing enumeration for clients, always obtain written authorization that specifies the scope and techniques allowed. For your own organization’s domains, enumeration is a standard security practice.
How many subdomains does a typical organization have?
The number varies enormously based on organization size and complexity. Small businesses may have 5 to 20 subdomains. Mid-size companies typically have 50 to 500. Large enterprises and technology companies routinely have thousands to tens of thousands. The key statistic is that most organizations discover 30 to 80 percent more subdomains than they initially expected when running comprehensive enumeration for the first time.
Can subdomain enumeration be detected by the target?
Passive techniques are undetectable because they query third-party data sources, not the target’s infrastructure. Active techniques — particularly DNS brute-forcing at high volume — can be detected through DNS query logging, intrusion detection systems, and rate limiting on authoritative DNS servers. Using moderate query rates, distributing queries across multiple resolvers, and mixing active enumeration with passive techniques minimizes detection risk.
What is the best tool for subdomain enumeration?
There is no single best tool — the best approach combines multiple tools and techniques. For quick passive discovery, Subfinder delivers fast results from many data sources. For comprehensive enumeration combining passive and active methods, Amass is the most full-featured open-source option. For organizations that need continuous monitoring without managing individual tools, automated platforms like Cyborux handle the entire workflow from discovery to risk assessment.
How do I prevent attackers from enumerating my subdomains?
Complete prevention is not possible — CT logs, passive DNS, and search engine indexing make subdomain discovery inherently possible. However, you can reduce your exposure by: using wildcard certificates to minimize CT log entries for individual subdomains, restricting sensitive subdomains behind VPN or IP allowlists, avoiding predictable subdomain naming conventions, and promptly decommissioning unused subdomains and their DNS records. The most effective defense is not to prevent enumeration but to ensure that every discoverable subdomain is hardened and monitored.
Conclusion
Subdomain enumeration is not an optional step in security — it is the foundation of external attack surface visibility. Every subdomain your organization operates is a potential entry point for attackers, and the subdomains you do not know about are the ones most likely to be exploited.
The techniques and tools available today make comprehensive subdomain discovery accessible to organizations of any size. Passive methods provide broad coverage with zero risk. Active techniques fill the gaps that passive methods miss. And automated platforms eliminate the operational overhead of managing multiple tools and correlating their output.
But discovery alone is not enough. The real value comes from turning enumeration results into action: building and maintaining a subdomain inventory, continuously monitoring for changes, remediating exposed or misconfigured services, and integrating subdomain awareness into your broader security operations.
Organizations that treat subdomain enumeration as a continuous process — not a one-time assessment — consistently maintain better visibility, respond faster to new exposures, and close the gaps that attackers depend on. The subdomains you discover today might include the one that would have been tomorrow’s breach headline.
Start with your root domains. Run comprehensive enumeration. Document what you find. Set up continuous monitoring. And act on every discovery — because if you can find it, so can an attacker.