The Most Common Attack Surface Findings: What Attackers See Before You Do
A company runs its first external attack surface scan. Within minutes, the results start coming in: twelve employee emails found in data breach databases, a domain that can be spoofed because DMARC is not enforced, three subdomains pointing to decommissioned services that anyone could claim, and PDF documents on the website leaking internal server names and network paths.
None of this required breaking into anything. Every piece of information was publicly accessible — the same data an attacker would collect in the first thirty minutes of reconnaissance.
This is what attack surface discovery reveals: the gap between what organizations think is exposed and what actually is. And the same categories of findings appear over and over, across industries, company sizes, and geographies.
This guide covers the most common findings from external reconnaissance, why each one matters, how attackers exploit them, and what you can do about them.
Email Exposures: The Starting Point for Most Attacks
Employee email addresses are the single most common finding in attack surface discovery — and the most consequential. They are the primary key that unlocks almost every other attack vector.
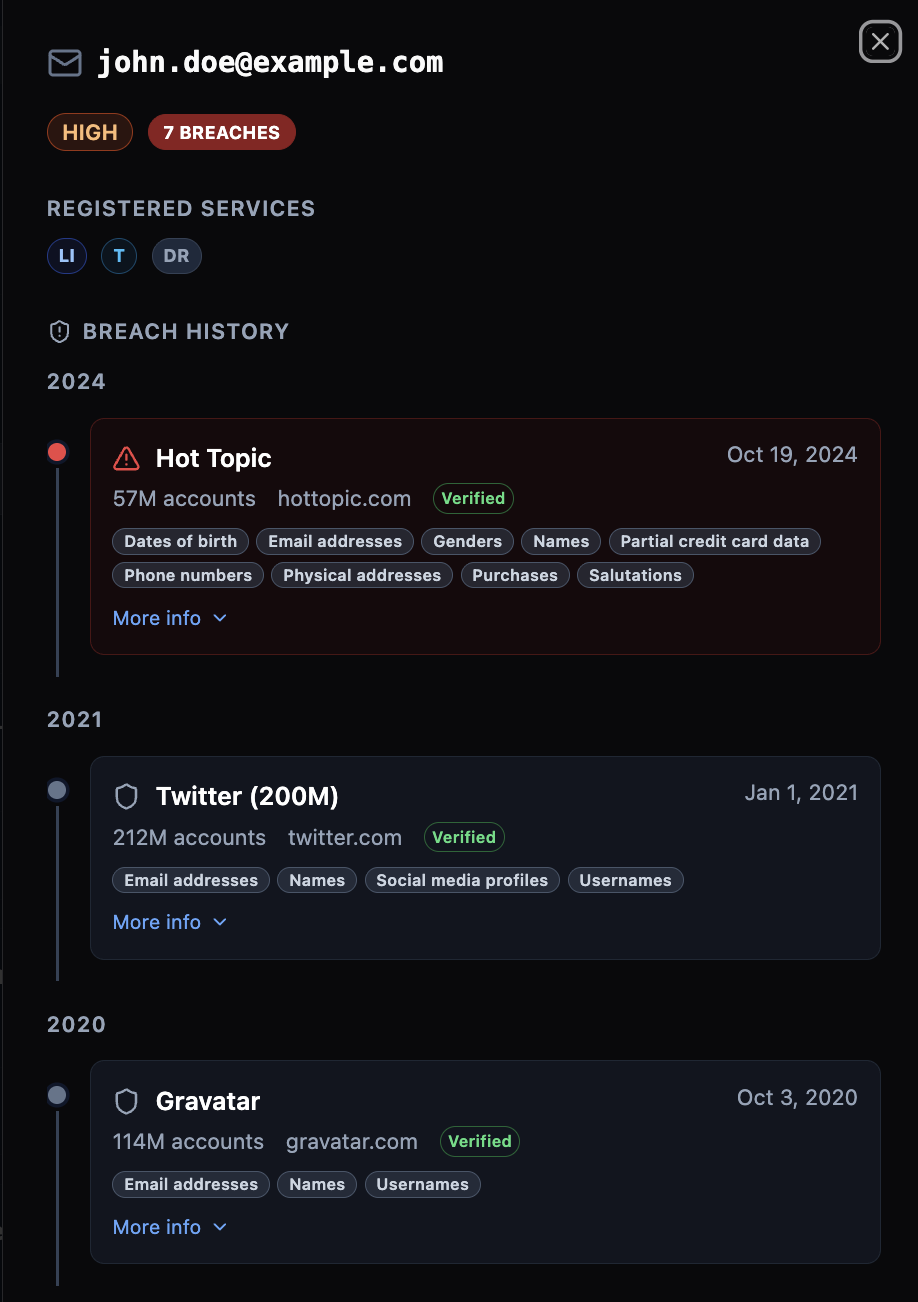
Breached Corporate Emails
When an employee’s work email appears in a data breach database, attackers know two things: the email address is valid, and the password associated with it (often included in the breach data) may still work somewhere. Credential reuse across services means a breached password from a compromised third-party platform can unlock corporate accounts.
The risk escalates with frequency. An email that appears in one old breach is concerning. An email in five or more breaches — especially recent ones — is a critical finding because the probability of active credential reuse is high.
Spoofable Email Domains
A domain without properly configured DMARC, SPF, and DKIM allows anyone to send emails that appear to come from that domain. No authentication, no warnings in the recipient’s inbox — just a convincing phishing email that passes every technical check.
This is not a theoretical risk. Business email compromise (BEC) attacks caused over $2.7 billion in losses in 2022 alone, according to the FBI’s Internet Crime Complaint Center. Most of these attacks exploit exactly this gap: a spoofable sender domain combined with enough public information about the target to craft a convincing message.
When email spoofability combines with identified executives (whose names, titles, and email patterns are publicly discoverable), the result is what security professionals call a phishing readiness chain — all the ingredients for a targeted spear phishing attack are already assembled.
Email Pattern Discovery
Attack surface scans frequently reveal the email pattern an organization uses: firstname.lastname@, first.last@, flast@, or similar. Once the pattern is known, an attacker can generate valid email addresses for any employee whose name they find on LinkedIn, the company website, or social media.
Subdomain Issues: The Forgotten Perimeter
Subdomains are consistently the most neglected part of an organization’s external perimeter. Companies add subdomains for projects, campaigns, testing environments, and third-party integrations — then forget about them.
Subdomain Takeover Vulnerabilities
When a subdomain’s DNS record (typically a CNAME) points to a service that has been decommissioned — an old Heroku app, an expired Azure instance, a cancelled GitHub Pages site — anyone can claim that service and serve content on the subdomain.
This is a critical finding because the attacker now controls a page under your legitimate domain. Phishing emails linking to login.yourcompany.com bypass every domain reputation check because the domain is real.
Exposed Internal Services
Subdomains like jenkins.company.com, grafana.company.com, staging.company.com, or vpn.company.com appear in attack surface scans far more often than they should. These are internal tools — CI/CD pipelines, monitoring dashboards, development environments — that were set up with public DNS records and never restricted.
An attacker finding phpmyadmin.company.com or redis.company.com resolving to a public IP has a direct path to critical infrastructure. Database services exposed to the internet are consistently rated as critical-severity findings.
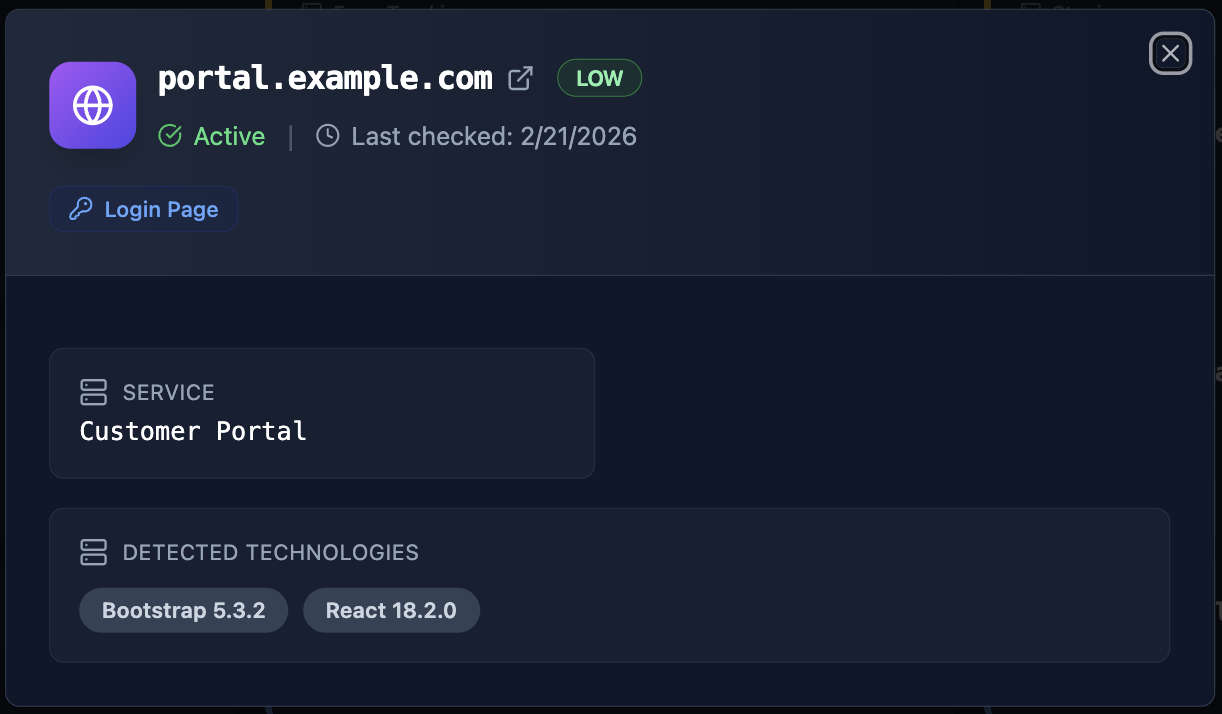
Authentication Endpoints
Login portals, SSO endpoints, and OAuth pages are legitimate services that need to be public. The risk is not their existence — it is their discoverability combined with other findings. When an attacker has breached employee credentials AND knows where the login page is, the path from reconnaissance to access is a straight line.
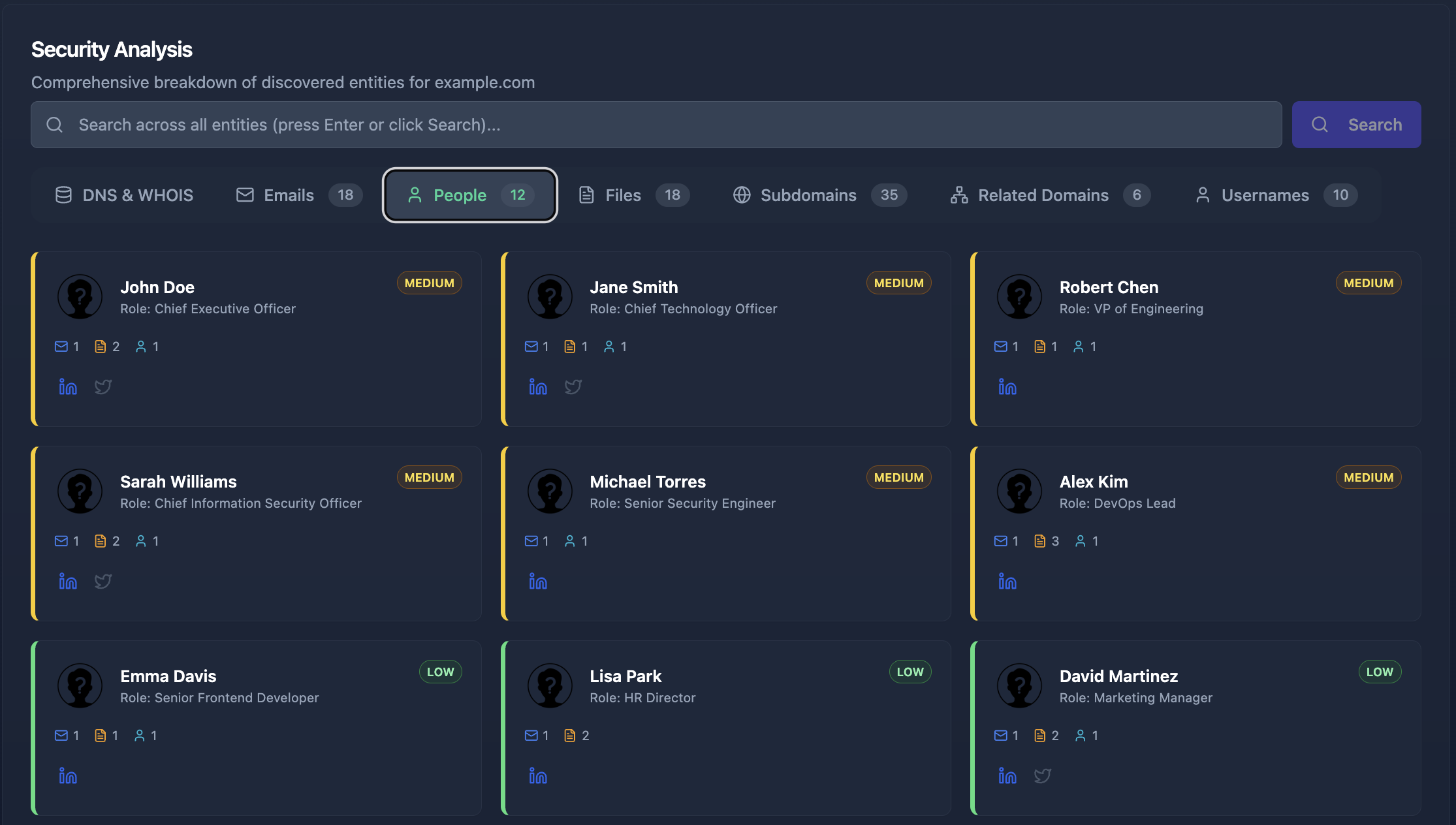
People and Personnel Exposure
Understanding who works at an organization — their roles, their digital footprint, and their exposure — is the foundation of targeted attacks. Attack surface discovery consistently reveals more about an organization’s people than most companies expect.
Executive Identification
C-suite executives, directors, and VPs are identified in virtually every scan. Their names, titles, and often their email addresses are publicly available through LinkedIn, press releases, conference presentations, and corporate websites.
This matters because executives are the primary targets for BEC attacks. An attacker impersonating the CEO to authorize a wire transfer does not need to hack anything — they need the CEO’s name, the CFO’s email, and a spoofable domain. All three are commonly discovered during reconnaissance.
IT and Security Personnel
When attack surface scans identify system administrators, DevOps engineers, or security team members, it signals to an attacker where the highest-privilege accounts are. Compromising an IT administrator’s credentials provides broader access than any other single account.
Digital Footprint Accumulation
Some employees accumulate an outsized digital footprint without realizing it: their email appears in multiple breaches, their username is consistent across a dozen platforms, their social profiles reveal project details and internal tooling, and files they authored contain metadata with internal infrastructure paths.
File and Document Metadata Leaks
Publicly accessible documents are a goldmine for reconnaissance. Every PDF, DOCX, XLSX, or PPTX file carries metadata that reveals information its authors never intended to share.
Internal Infrastructure in Metadata
Document metadata frequently contains:
- Internal IP addresses (10.x.x.x, 192.168.x.x, 172.16-31.x.x) — revealing the internal network structure
- Server names and UNC paths (\\FILESERVER01\shared) — exposing Active Directory naming conventions
- Software versions — showing exactly which tools and versions are running internally
- Author usernames — often matching Active Directory usernames used for authentication
A single PDF on a company’s public website can reveal more about their internal infrastructure than hours of active scanning.
Sensitive File Types
Configuration files (.env, .config), database dumps (.sql, .bak), cryptographic material (.key, .pem, .pfx), and VPN configurations (.ovpn, .rdp) occasionally appear in public web directories. These are critical findings — they may contain credentials, connection strings, or private keys.
TLS/SSL and Encryption Weaknesses
Transport Layer Security protects data in transit. When it is misconfigured, absent, or outdated, the consequences range from passive eavesdropping to active man-in-the-middle attacks.
Missing HTTPS
Domains and subdomains serving content over plain HTTP — without any TLS encryption — are still found regularly. All traffic including credentials, session tokens, and personal data is transmitted in cleartext.
Weak TLS Configurations
TLS assessments reveal grades from A+ (excellent) through F (failing). Common issues include:
- Legacy protocols — TLS 1.0 and 1.1 are deprecated with known vulnerabilities, yet many organizations still support them for backward compatibility
- Known vulnerabilities — Heartbleed, POODLE, BEAST, DROWN, and other protocol-level attacks affect servers with outdated configurations
- Missing HSTS — Without HTTP Strict Transport Security, browsers can be tricked into downgrading HTTPS connections to plain HTTP
Missing Security Headers
Beyond TLS, HTTP security headers form an additional defense layer. Missing Content-Security-Policy (CSP) enables cross-site scripting. Missing X-Frame-Options enables clickjacking. Server headers that disclose software versions give attackers a technology fingerprint without any active probing.
Technology Stack Exposure
Every piece of software running on an organization’s external infrastructure — web servers, frameworks, CMS platforms, JavaScript libraries — is a potential entry point when vulnerabilities are discovered.
Outdated and End-of-Life Software
Technology detection reveals the exact versions of software running on each subdomain. When those versions have known CVEs (Common Vulnerabilities and Exposures) — especially with available exploits — the finding becomes critical.
End-of-life software is even worse: no patches will ever be released, so any discovered vulnerability remains permanently exploitable.
Debug and Development Tools in Production
Debug toolbars, development consoles, and diagnostic endpoints that were left active in production appear in a surprising number of scans. These tools often bypass authentication, expose source code, and provide direct code execution capabilities.
See What Your Attack Surface Actually Looks Like
Run a full reconnaissance on your domain in minutes. Discover breached emails, vulnerable subdomains, exposed infrastructure, and leaked files — before an attacker does.
Get Started FreeBuilt for security teams, IT managers, and consultants.
How Findings Combine: Attack Chains
Individual findings have their own severity. But the real risk emerges when multiple findings combine into attack chains — end-to-end paths that an attacker can follow from reconnaissance to compromise.
The Credential Stuffing Chain
Ingredients: Leaked corporate emails + exposed passwords + active authentication endpoint
When breached credentials are combined with a discoverable login page, the attack writes itself. The attacker takes the leaked email and password, navigates to the login endpoint, and attempts access. If the employee reused their password (statistically likely), the attacker is in.
The Phishing Readiness Chain
Ingredients: Spoofable email domain + identified executives + discoverable email pattern
The attacker crafts an email from the CEO (spoofable domain, no DMARC enforcement), addressed to the CFO (identified via LinkedIn, email pattern known), requesting an urgent wire transfer. Every component of this attack was assembled from publicly available data.
The Subdomain Takeover + Phishing Chain
Ingredients: Takeover-vulnerable subdomain + identified personnel
The attacker claims login.company.com (dangling CNAME), sets up a convincing login page, and sends employees a link. The domain is legitimate. The SSL certificate is valid (the attacker created it). The page looks identical to the real SSO. The success rate for this attack is dramatically higher than traditional phishing because every trust signal checks out.
What To Do About It
The findings described in this guide are not hypothetical. They are what Cyborux discovers during automated domain analysis — and they appear across organizations of every size.
Prioritize by Attack Chain, Not Individual Severity
A medium-severity finding that completes a critical attack chain is more urgent than an isolated high-severity finding. Focus remediation on breaking the chains: if you cannot fix the spoofable domain immediately, ensure your executives’ emails are not discoverable. If you cannot patch every subdomain, decommission the ones with takeover risk first.
Automate Continuous Monitoring
Attack surfaces change constantly. New subdomains are created, new breaches are published, employees change roles. A point-in-time assessment becomes stale within weeks. Continuous monitoring catches new exposures as they appear — before attackers find them.
Reduce the Digital Footprint
Many findings exist because information was published that did not need to be. Reducing your organization’s digital footprint — scrubbing document metadata, removing unnecessary public DNS records, limiting employee information on corporate websites — eliminates findings at the source.
Connect Intelligence to AI for Speed
The volume of findings across a growing attack surface can overwhelm manual review. Connecting an attack surface intelligence platform to an AI assistant through MCP lets you investigate, correlate, and prioritize findings conversationally — asking questions like “Which executives have breached emails and what authentication endpoints are exposed?” instead of manually cross-referencing spreadsheets.
Conclusion
The findings in this guide are not edge cases. They are the baseline reality for most organizations: breached employee emails, spoofable domains, forgotten subdomains, leaked document metadata, weak TLS configurations, and outdated software. They appear in scan after scan, industry after industry.
What makes them dangerous is not any single finding in isolation — it is the combinations. A breached email is concerning. A breached email plus an exposed login page plus a spoofable domain is an attack chain that requires nothing more than patience to exploit.
The first step is visibility. You cannot fix what you cannot see. Run a scan on your domain with Cyborux, and within minutes you will know exactly what an attacker would find.
The question is not whether these exposures exist. It is whether you find them first.